Giving A fast and powerful reporting program when anomalous or malicious activity occurs, which permits the menace to get passed up the stackAs an example, an IDS could anticipate to detect a trojan on port 12345. If an attacker had reconfigured it to make use of a different port, the IDS may not be able to detect the existence on the trojan.Abbrev
 Tahj Mowry Then & Now!
Tahj Mowry Then & Now!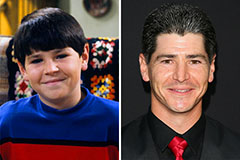 Michael Fishman Then & Now!
Michael Fishman Then & Now! Michael C. Maronna Then & Now!
Michael C. Maronna Then & Now! Danielle Fishel Then & Now!
Danielle Fishel Then & Now! Jaclyn Smith Then & Now!
Jaclyn Smith Then & Now!